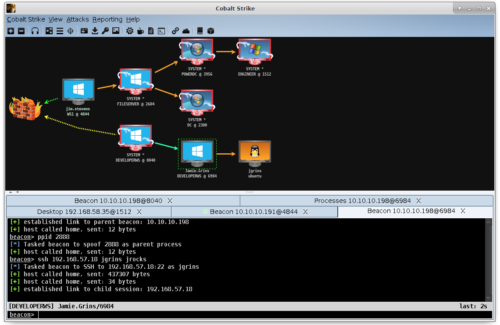
Evading Windows Defender with Cobalt Strike and Detecting the Undetected | by Soteria Cybersecurity | Soteria-Security

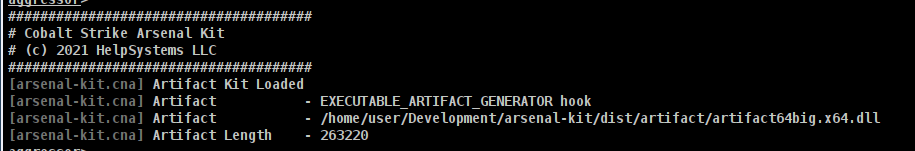
FalconFeedsio on X: "A user on hackers forum is promoting the sale of package of tools. The package includes Cobalt Strike, Custom UDRL, Custom Artifact Kit, Custom LSASS, Custom Profile, Custom UAC

FalconFeedsio on X: "A user on hackers forum is promoting the sale of package of tools. The package includes Cobalt Strike, Custom UDRL, Custom Artifact Kit, Custom LSASS, Custom Profile, Custom UAC
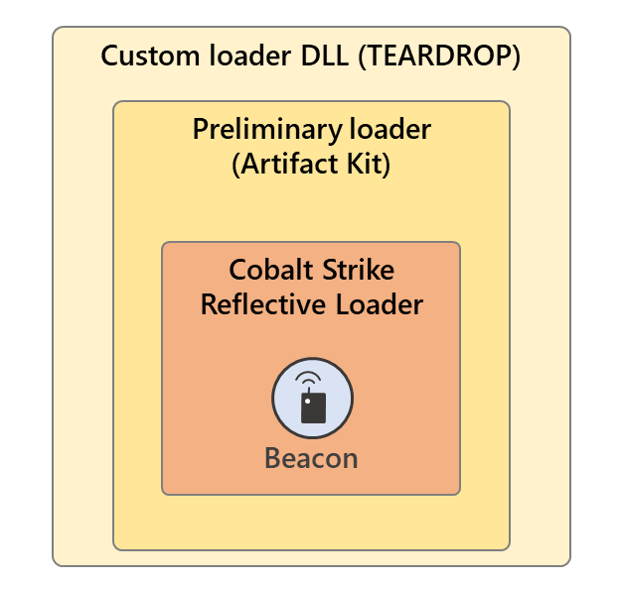
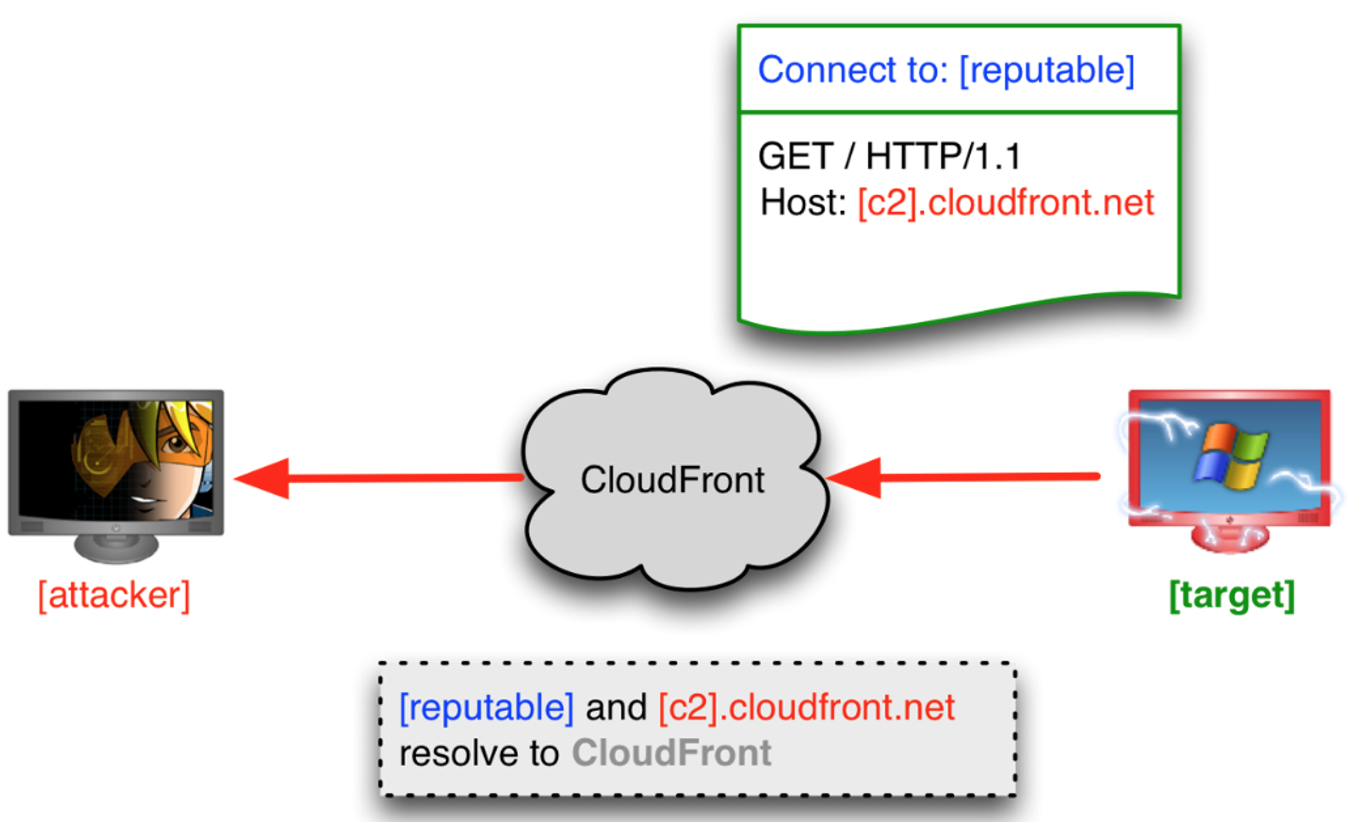
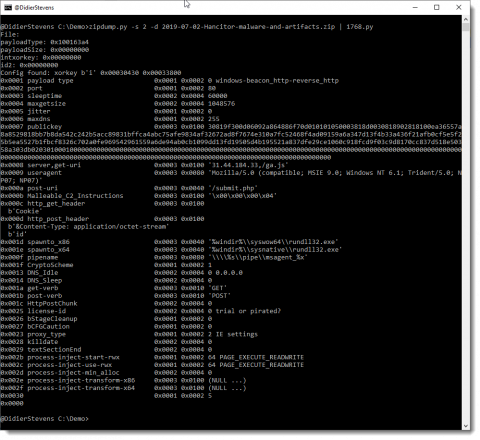
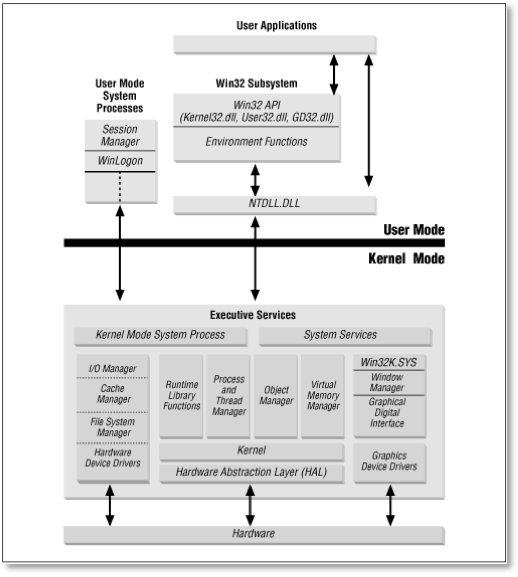
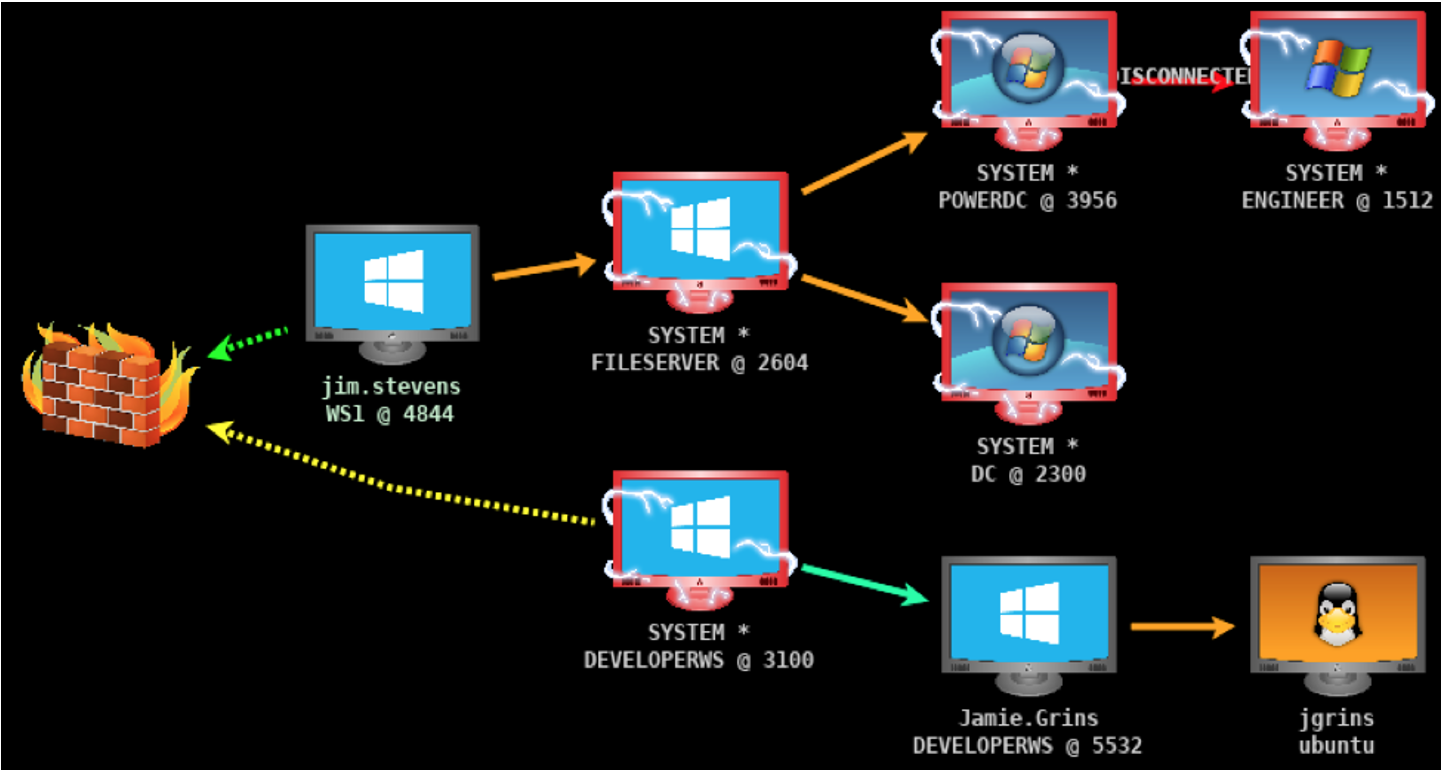
Deep dive into the Solorigate second-stage activation: From SUNBURST to TEARDROP and Raindrop | Microsoft Security Blog